Tags
Tags management
DCT powers data governance with tags. These key-value pairs can be used to associate any business-level data with any Delphix object, to drive greater intelligence in automation, administrative workflows, data access, and reporting. Advanced search for tags is available.
Tags are individual attributes on every object exposed in DCT; from VDBs, to compliance jobs, and even users. There are no limits on tag count per object and character limits are set for flexibility to enable robust grouping.
Administrative tagging
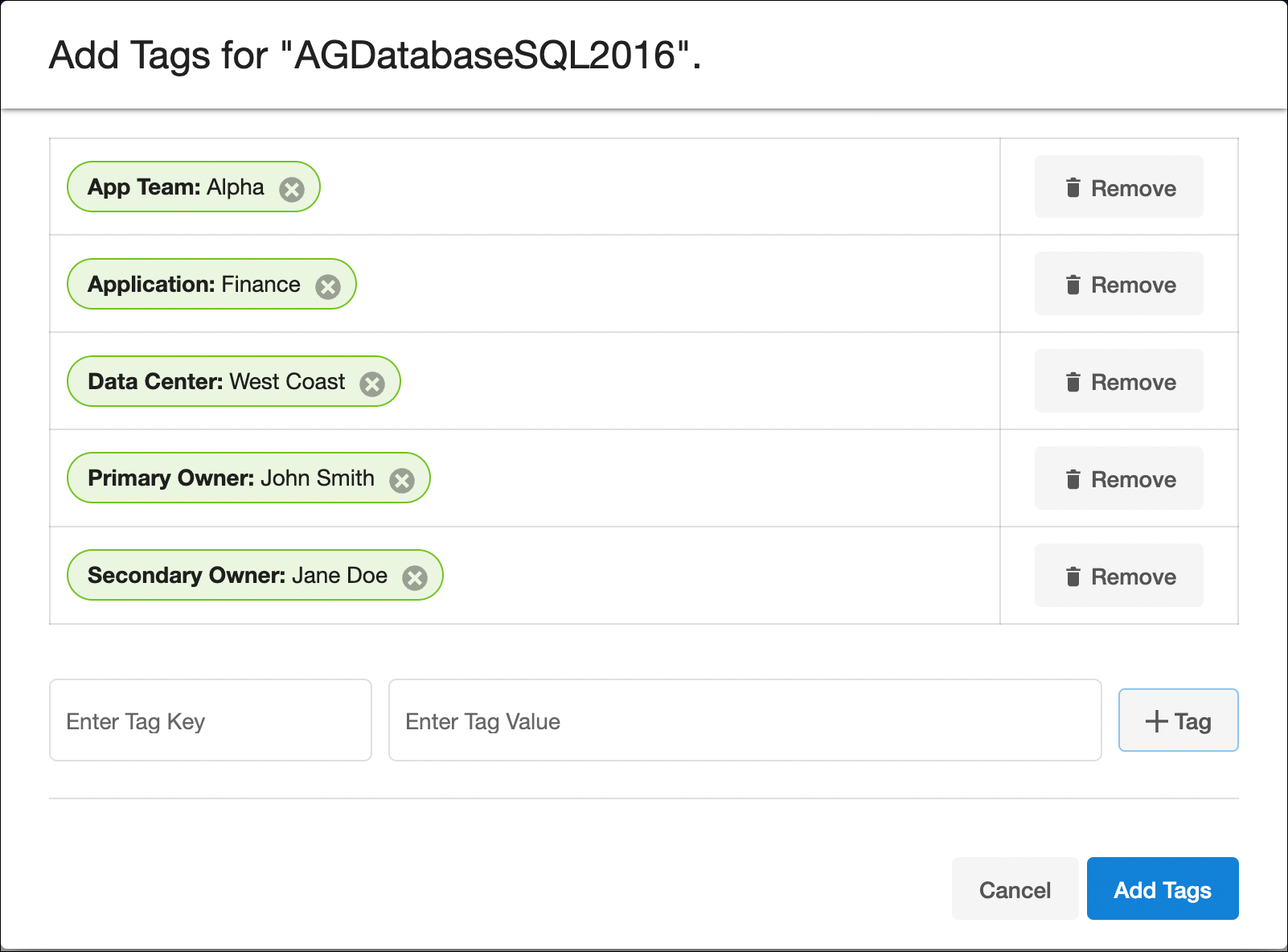
Tags can be managed from the UI by selecting “View Tags” for a particular object on its global list page. The below example shows the tag configuration screen for a dSource “AGDatabaseSQL2016” and multiple tags have been added to characterize that particular object:
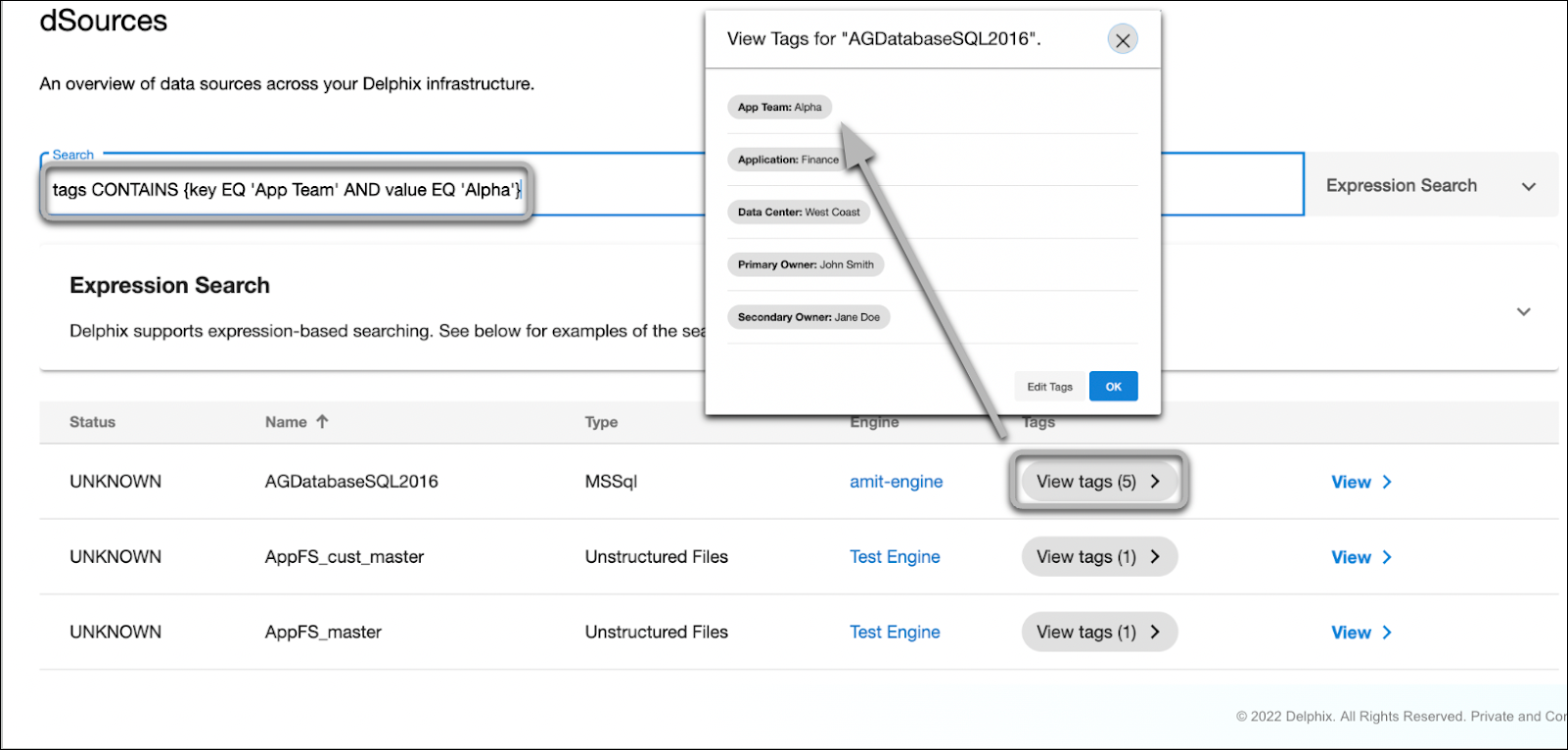
DCT tags enable complex searching to enable intelligent reports. A demonstration using the above example dSource and using expression-based search to filter dSources with the {App Team: Alpha} tag.
Tags powering attribute-based Access Control
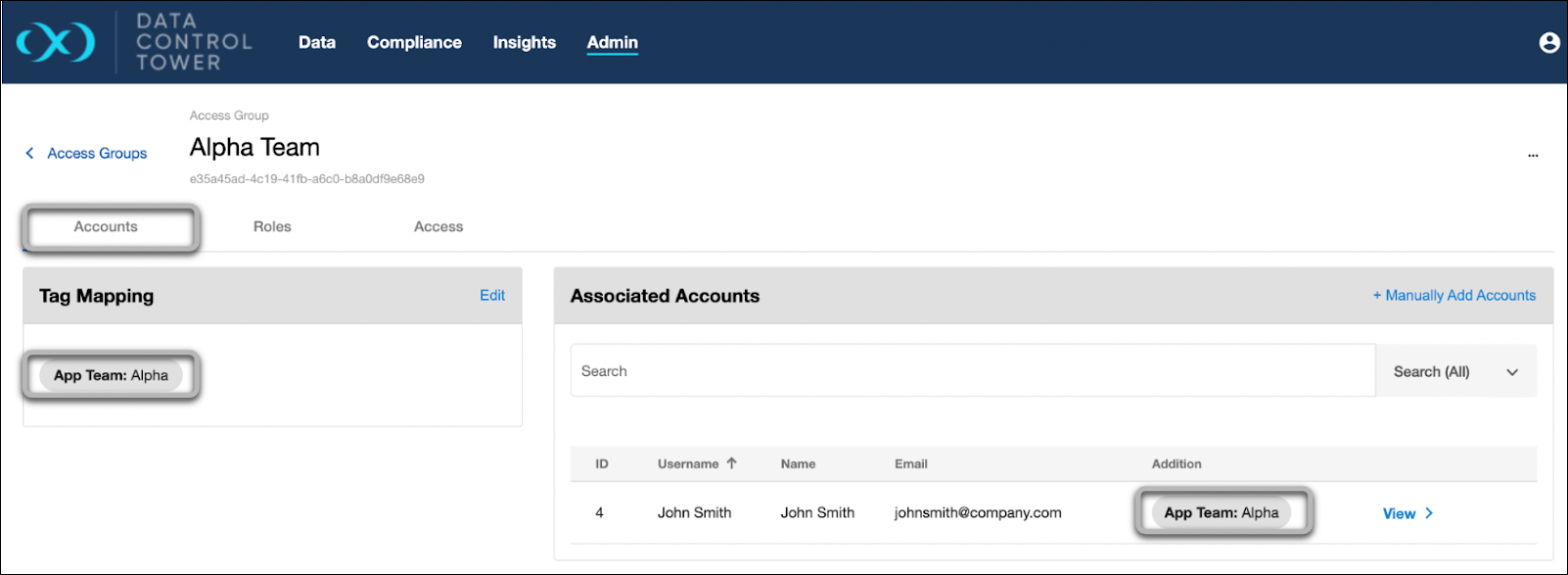
Tags also power the DCT permissions system for both Accounts (users) and Role Scopes (object entitlements). The below example shows an Access Group (Alpha Team) with the Accounts tab on display. Notice that the accounts tab has {App Team: Alpha} under “tag mapping”, which automatically attributes any users with the {App Team: Alpha} tag.
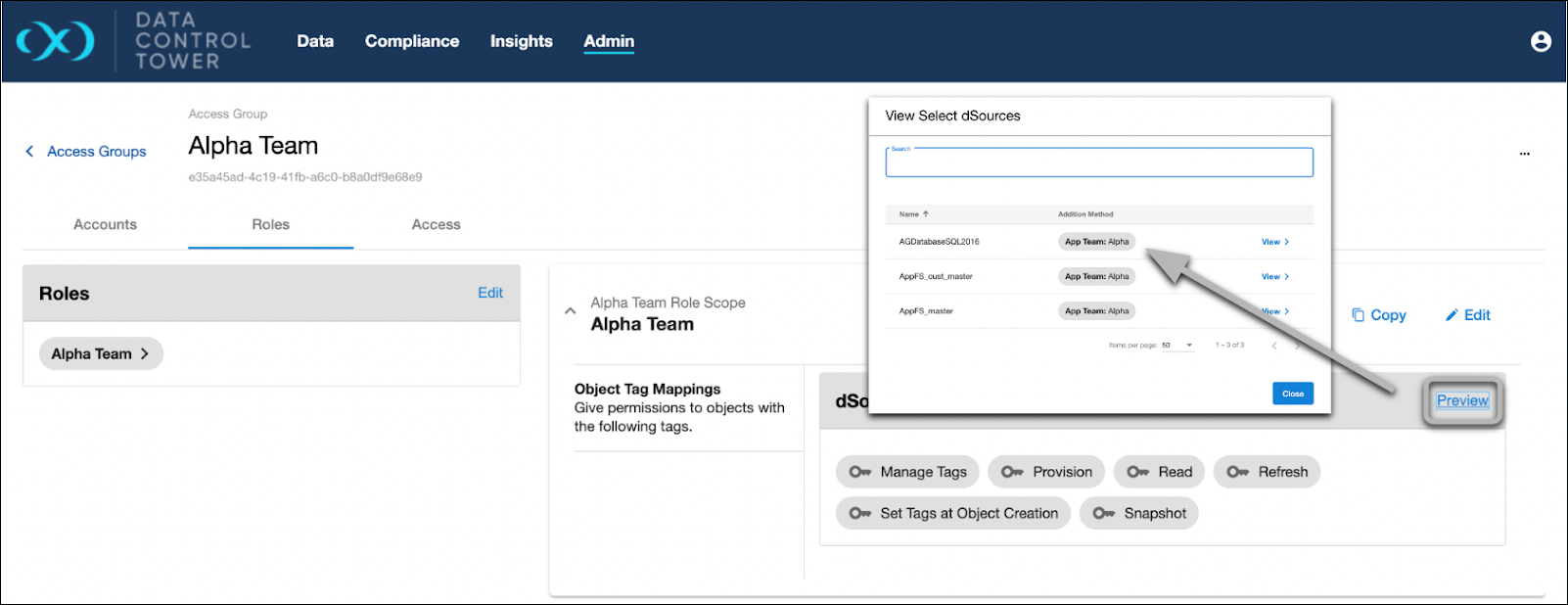
The same goes for Scoped Roles under the “Roles” tab. The Alpha Team role has been mapped to the {App Team: Alpha} tag and all dSources with that same tag are automatically attributed.
Tag Assignment
First, navigate to the Admin > Accounts tab and select an existing Account or feel free to create another one. Once selected, add a custom Tag such as "Team: Alpha”. If one already exists on the Account, such as login_groups, remember it.
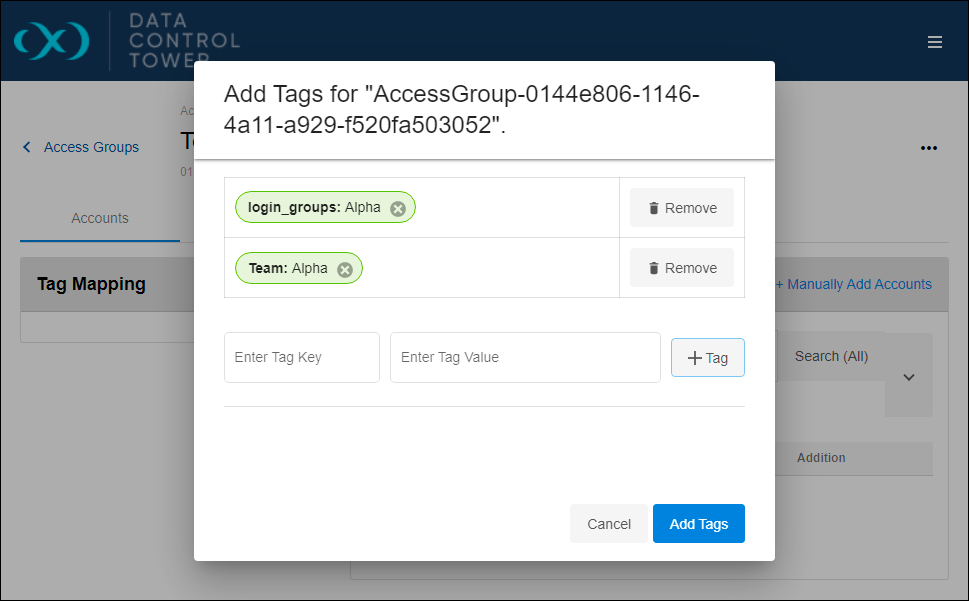
Next, navigate back to the Access Group, select the Tag Mapping’s Edit button, and specify that same Key: Value pair. It might look similar to the screenshot below.
In this example, “Team: Alpha” and “login_groups: Alpha” were added through the Access Group’s Tag Mapping widget. If configured successfully, your Access Group might look similar to thescreenshot below. If you remove the Access Group or Account’s tag, you will see Account automatically removed from this listing.
The “login_groups” tag functions identically to a custom tag within the Access Group. Again, the only difference is that it's automatically assigned to the Account.
This section taught us how to organize Accounts into different groups. This allows us to keep permission sets separated. Feel free to experiment with new Access Groups, Tags, and Accounts.