Discovery overview
Sensitive data discovery identifies sensitive data and proposes masking rules to protect it, ensuring privacy and compliance with data protection regulations.
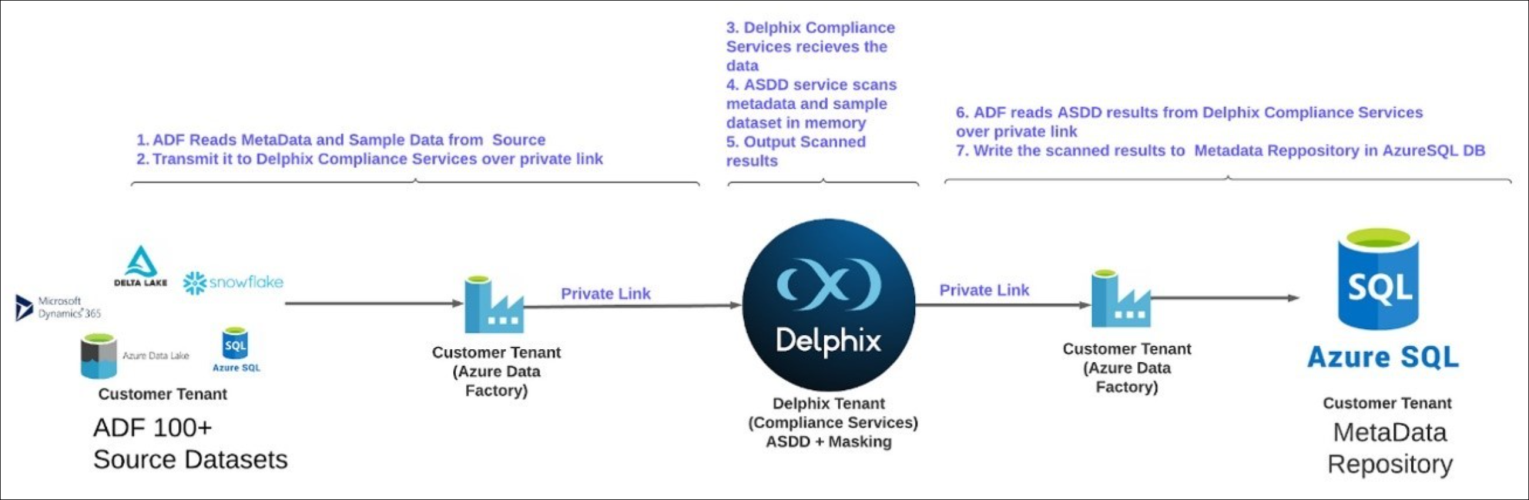
The overall process flow diagram is shown below that consists of the following steps:
-
ADF reads metadata and sample data from the source connector.
-
One of the steps in the ADF pipeline transmits the data to the Delphix Compliance Services:
-
The data transmission can happen over a private link
-
Or via the publicly available external gateway
-
-
Delphix Compliance Services receives the data.
-
The metadata and the sample dataset are scanned by the discovery service to identify sensitive fields, suggesting any masking rules for the identified fields.
-
ADF reads the results of the discovery from DCS over the private link.
-
Finally, the scanned results are written to the metadata repository in an Azure SQL DB.